As the Tunjangan Hari Raya (THR) holiday allowance period approaches, digital transactions across Indonesia surge sharply. People wait for transfer notifications, shopping activity rises, travel tickets are booked, and funds move faster than usual. Behind this wave of activity, however, lies a growing threat of fraud that does not occur randomly.
In the Kasisolusi podcast titled “80% Penipuan OTP Naik Saat Musim THR!? Ini Modus Phishing yang Bikin Rekening Ludes!!”, Niki Luhur, Founder and Group CEO of VIDA, emphasized that this surge is far from coincidental.
“Fraud today is not just about technology, it is about timing,” said Niki. “When people are waiting for their THR and incoming notifications, a single convincing fake link can immediately trigger an account takeover or data theft. The discipline to not click impulsively sounds simple, but the impact is critical.”
Liquidity distribution moments such as THR payments and monthly paydays create ideal conditions for criminals. When liquidity and trust converge at the same time, risk rises sharply.
Digital Fraud Is No Longer Sporadic, It Is Organized
Fraud tactics continue to evolve. AI deepfakes can now replicate faces and voices with increasing precision. Fake Base Transceiver Stations (fake BTS) allow fraudulent messages to be sent in bulk while appearing to come from official institutions. Malware disguised as APK files can infiltrate devices and remotely monitor user activity.
VIDA emphasizes that digital fraud is no longer sporadic. It is becoming increasingly organized and industrialized.
“Fraud always adapts. Criminals exploit security gaps, weaknesses in public digital literacy, and specific moments of opportunity to carry out their attacks,” Niki explained.
Globally, the World Economic Forum has already identified cyber related fraud and identity theft as among the world’s major risks. This indicates that the issue is no longer just an individual problem but a systemic threat to the stability of the digital economy.
THR Disbursement Becomes a Prime Target
Based on VIDA’s internal data throughout 2025 and findings from the VIDA 2026 SEA Digital Identity Fraud Outlook Whitepaper, the most significant spikes in fraud occur right before and during THR disbursement periods.
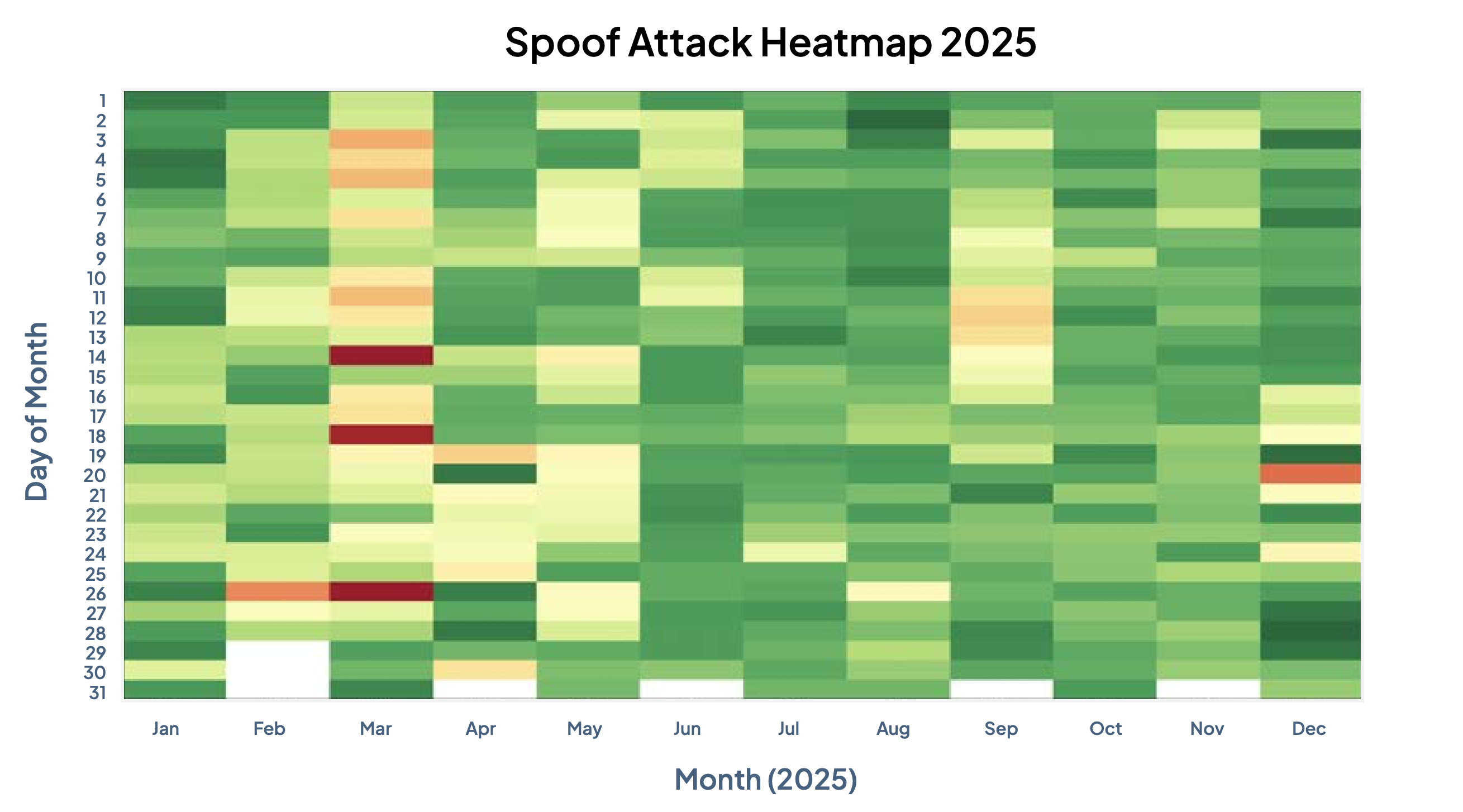
This pattern aligns with warnings from Indonesia’s Ministry of Communication and Digital Affairs, the Financial Services Authority (OJK), and Bank Indonesia, which identify the Ramadan to Eid period as a high risk phase for digital payment systems.
There are three main reasons why this period becomes a prime target for fraudsters.
First, people are waiting for transfer notifications and bonuses. Any message related to balance updates or transaction confirmations feels relevant and therefore less suspicious.
Second, transaction activity rises sharply. With frequent shopping, transfers, and ticket purchases, fraudulent messages can easily blend in with legitimate notifications.
Third, emotional conditions make people more reactive. Euphoria, urgency, and the pressure to act quickly lower the threshold for suspicion.
Criminals understand these dynamics well. Fraud today is not simply about deception. It is also about synchronizing attacks with the rhythm of economic activity and public psychology.
Phishing, Fake BTS, and Malware Continue to Evolve
Currently, the two most common fraud methods in Indonesia are phishing or smishing and malware attacks.
Phishing lures victims into clicking malicious links and entering sensitive data such as usernames, passwords, or OTP codes. These messages often appear as package delivery notifications, fake Ramadan promotions, or bank alerts.
Meanwhile, fake BTS attacks allow messages to appear as though they were sent directly from official financial institution channels, including banks.
Malware, on the other hand, typically infiltrates devices through APK files disguised as relevant documents, such as shipping confirmations, invitations, or administrative files. Once installed, these malicious applications can monitor devices, access passwords, and control sensitive information without the victim’s awareness.
Despite their different techniques, these fraud methods share the same goal: obtaining user credentials.
This reality highlights a critical point. Passwords alone are no longer sufficient to secure digital identities in today’s complex threat landscape.
Passwords Alone Are No Longer Enough
Niki explained that digital identity essentially consists of three layers: what you know, what you have, and who you are. “What you know” includes information known by the user, such as passwords or security questions. “What you have” refers to devices owned by the user, such as mobile phones or authentication tokens. “Who you are” relates to unique biometric characteristics, such as facial features, voice, or fingerprints.
“Passwords and OTPs can no longer be the only verification method,” Niki said. “The devices we use and our biometric identities must also be protected and used as additional security layers.”
For this reason, a layered defense approach is increasingly critical. Protection cannot rely on a single checkpoint. Systems must secure devices, verify the presence of real humans through biometrics, and integrate multiple layers of defense into a unified system.
Fraud today does not occur in isolation. It exploits devices, credentials, and human psychology within the same attack flow. Defense must therefore be integrated as well.
As the THR disbursement period approaches, prevention is no longer just about strengthening system security. It is also about protecting families from unseen financial risks and preserving trust in the digital space.
This moment serves as a reminder that digital security is not merely a technical issue. It is a shared responsibility in safeguarding trust across the digital economy.
Read more VIDA whitepaper at https://vida.id/wheresthefraud

.png)