Browse our latest articles and resources

How to Enable Two-Step Verification and Improve Account Security
Know what is 2-step verification and learn how to enable two-step verification to strengthen account security and reduce the risk of unauth...
May 30, 2026

Employee Onboarding: Why It Matters and How to Build an Effective Process
Employee onboarding helps new hires adapt faster and improve productivity. Learn why onboarding matters and how to create an effective proc...
May 29, 2026
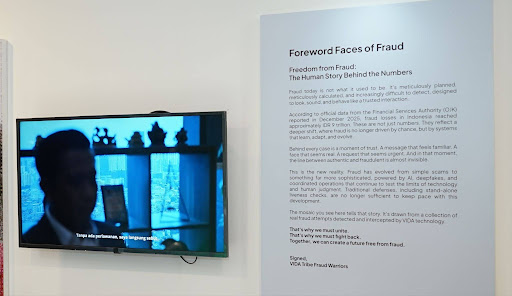
The Human Cost Behind Indonesia’s Digital Fraud
Behind every digital fraud statistic are victims who lose their savings, identities, and sense of security. Through “Faces of Fraud,” VIDA ...
May 20, 2026

What is a DDoS Attack? How It Works and How to Prevent It
A DDoS attack can overwhelm websites and online services with massive traffic. Learn how it works, common warning signs, and ways to reduce...
May 01, 2026

Phishing Attack: Definition, Examples, and Prevention Tips
Phishing is a common online scam used to steal sensitive information. Learn what it is, see real examples, and discover practical ways to a...
April 30, 2026

Behavioral Biometrics: How It Works and Why It Matters for Fraud Prevention
Behavioral biometrics analyzes user behavior patterns to detect fraud in real time. Learn how it works and why it’s essential for modern di...
April 30, 2026
The World of VIDA: Invisible Infrastructure Behind Digital Identity
Explore how invisible digital identity infrastructure protects everyday transactions while strengthening fraud awareness in Indonesia’s dig...
April 07, 2026

The Hidden Pattern Behind Rising Digital Transactions and Fraud
Digital fraud tends to rise when transaction activity surges. VIDA’s data reveals that periods such as THR disbursement and payday have bec...
March 26, 2026

e-Sign is Now Available in Malaysia
Malaysia e-Sign is here. Sign documents legally on the web, securely and compliantly.
March 17, 2026

From Petty Crime to Industrialized Operations: Key Insights from Endgame Podcast on Systemic Fraud
Fraud is no longer isolated crime. It has become systemic, industrialized, and embedded in digital infrastructure across Southeast Asia. In...
March 15, 2026

Bonus Season Is Prime Time for Fraud, and One Click Could Cost You Everything
As the Tunjangan Hari Raya (THR), Indonesia’s mandatory holiday allowance paid ahead of major religious holidays, approaches, digital trans...
March 12, 2026

How to Apply for UMKM Assistance Online and Tips to Pass Verification
Want to start a small business (UMKM)? Learn the complete guide to applying for UMKM assistance online, along with practical tips to help y...
March 02, 2026
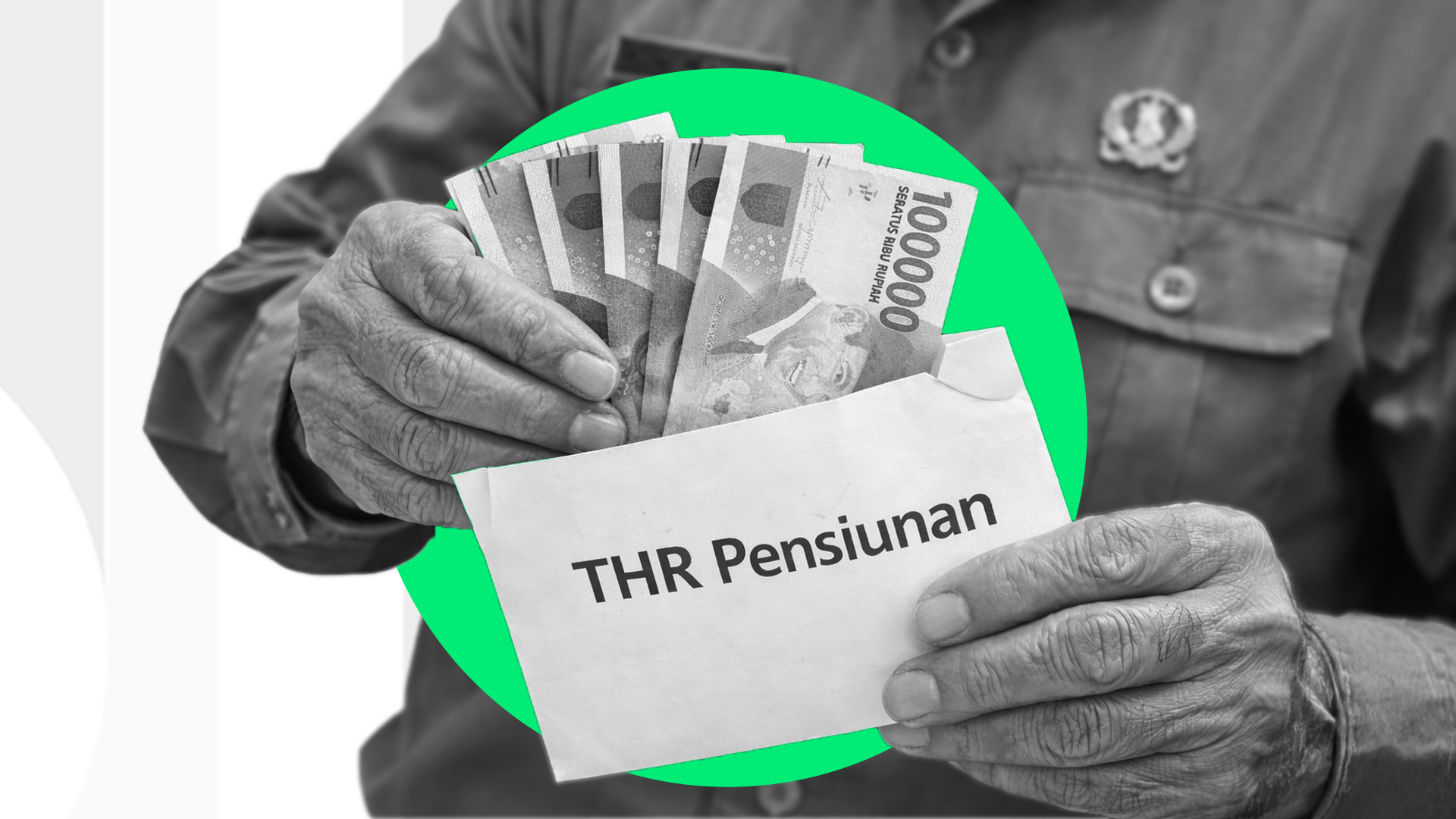
Disbursement of THR for Retired Civil Servants: Schedule and Mechanism
When can retired civil servants (PNS) receive their THR? Here’s a complete guide covering the definition, schedule, components, and legal b...
February 24, 2026

How to Calculate THR: Complete Guide with Formulas and Examples
Want to know how much THR (Holiday Allowance) you’ll receive? Here’s a complete guide on calculating THR for employees, including prorated ...
February 23, 2026

Types of Taxes and the Convenience of the Coretax System
Learn about the different types of taxes in Indonesia, their benefits, and how Coretax supports secure, integrated tax reporting.
February 11, 2026

Best Health Insurance: Types and How to Manage Them
Unpredictable medical costs make it essential to consider health insurance. Here's how to choose the right insurance based on types, benefi...
February 05, 2026

Best Car Insurance: Types and How to Manage Them
Choosing the best car insurance usually comes down to your needs and your vehicle's risk profile. Here's a guide to help you pick the right...
February 05, 2026

Examples of Digital Documents You Should Know About
Learn about the different types of digital documents you'll frequently use in the workplace — from examples and risks to how to keep them l...
February 04, 2026

A Complete and Easy-to-Follow Guide to Filing a Car Insurance Claim
Confused about how to file a car insurance claim? Check out this complete guide covering the step-by-step process, required documents, and ...
February 04, 2026
.jpeg)
The New Digital Crime Economy: Why AI-Driven Fraud Syndicates are the 'Startups' of the New Era
AI-powered attacks—such as large-scale deepfake attacks, synthetic identity fraud, and automated device farms—are effectively eroding trad...
February 03, 2026
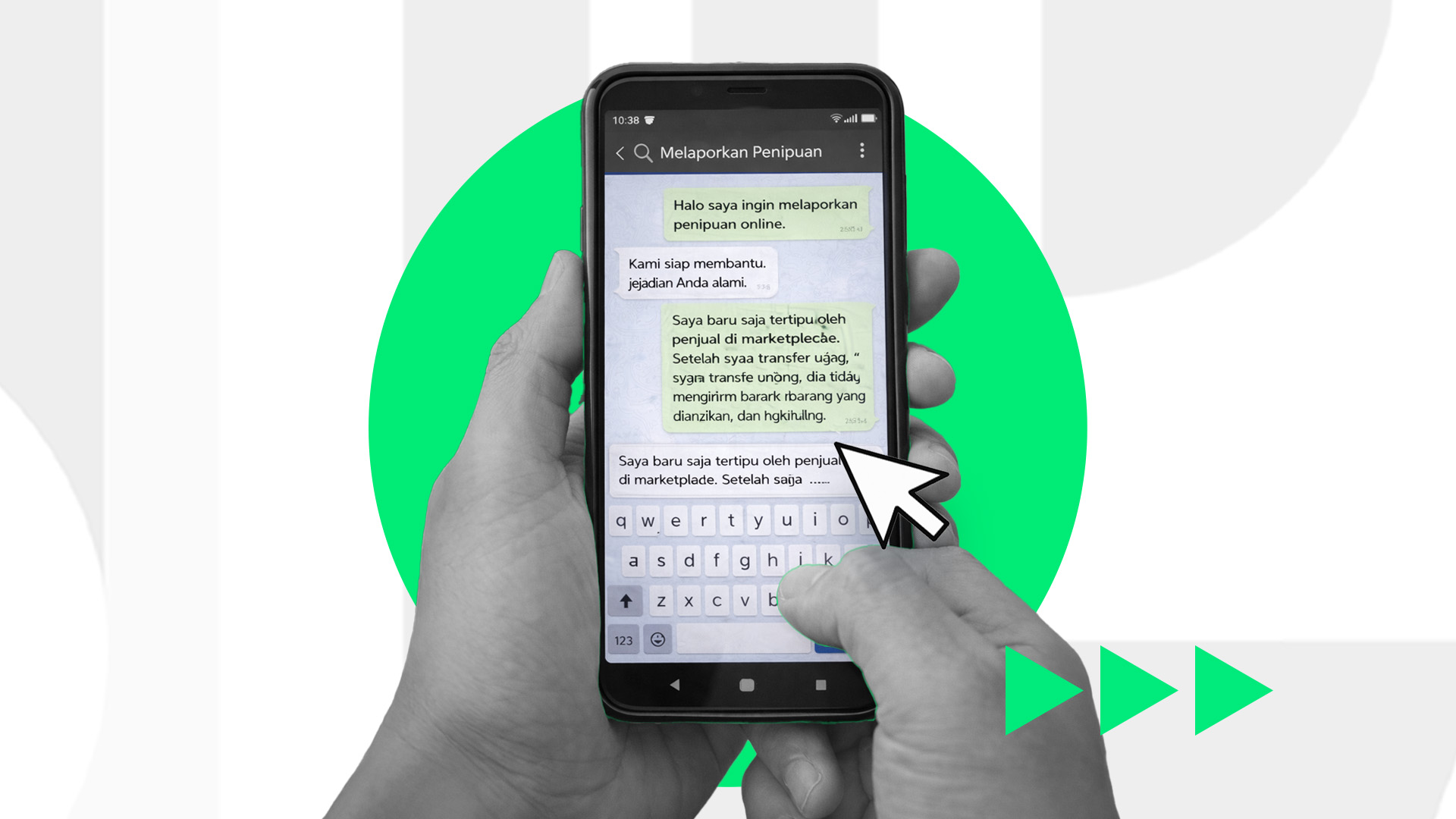
Online Scam Reporting: What to Do and Where to Report It
Been scammed online? Learn the important steps to take, what evidence to prepare, and where to report online fraud so it can be handled mor...
February 02, 2026

How to Log In to Coretax DJP, Activate Your Account, and Access the Latest Tax System
A complete guide to accessing the Coretax DJP system for taxpayers, including account activation, secure login tips, and common issues you ...
February 02, 2026

How to Check Your NPWP in Coretax: Methods, Status Meanings, and Common Issues
A complete guide to checking your NPWP in Coretax for taxpayers in Indonesia. Learn the step-by-step process, understand NPWP status meanin...
February 01, 2026

Online Scam Tactics: How to Recognize and Avoid Them
Digital scams are becoming increasingly sophisticated and harder to detect. Learn the common patterns, potential risks, and simple steps yo...
February 01, 2026
Got a Question?
We're Here to Help!