Behavioral Biometrics: How It Works and Why It Matters for Fraud Prevention
Behavioral biometrics analyzes user behavior patterns to detect fraud...
Fake email attacks are becoming more sophisticated through phishing, spoofing, and identity impersonation. Learn the definition, how it wor...
June 08, 2026
Fake GPS tools can alter a device's location, making fraudulent activity harder to detect. Learn how GPS spoofing works, why fraudsters use...
June 07, 2026

Behavioral biometrics analyzes user behavior patterns to detect fraud...
April 30, 2026
Advanced technology like liveness detection can distinguish real...
October 18, 2025

Be aware of the types of personal data—such as your name, national ID...
October 04, 2025

Be aware of the most common online fraud cases such as phishing, SIM...
July 30, 2025
Learn about the latest fraud cases that exploit AI, APK files, and...
July 16, 2025
A staggering 16 billion passwords have been leaked! This proves that...
June 23, 2025

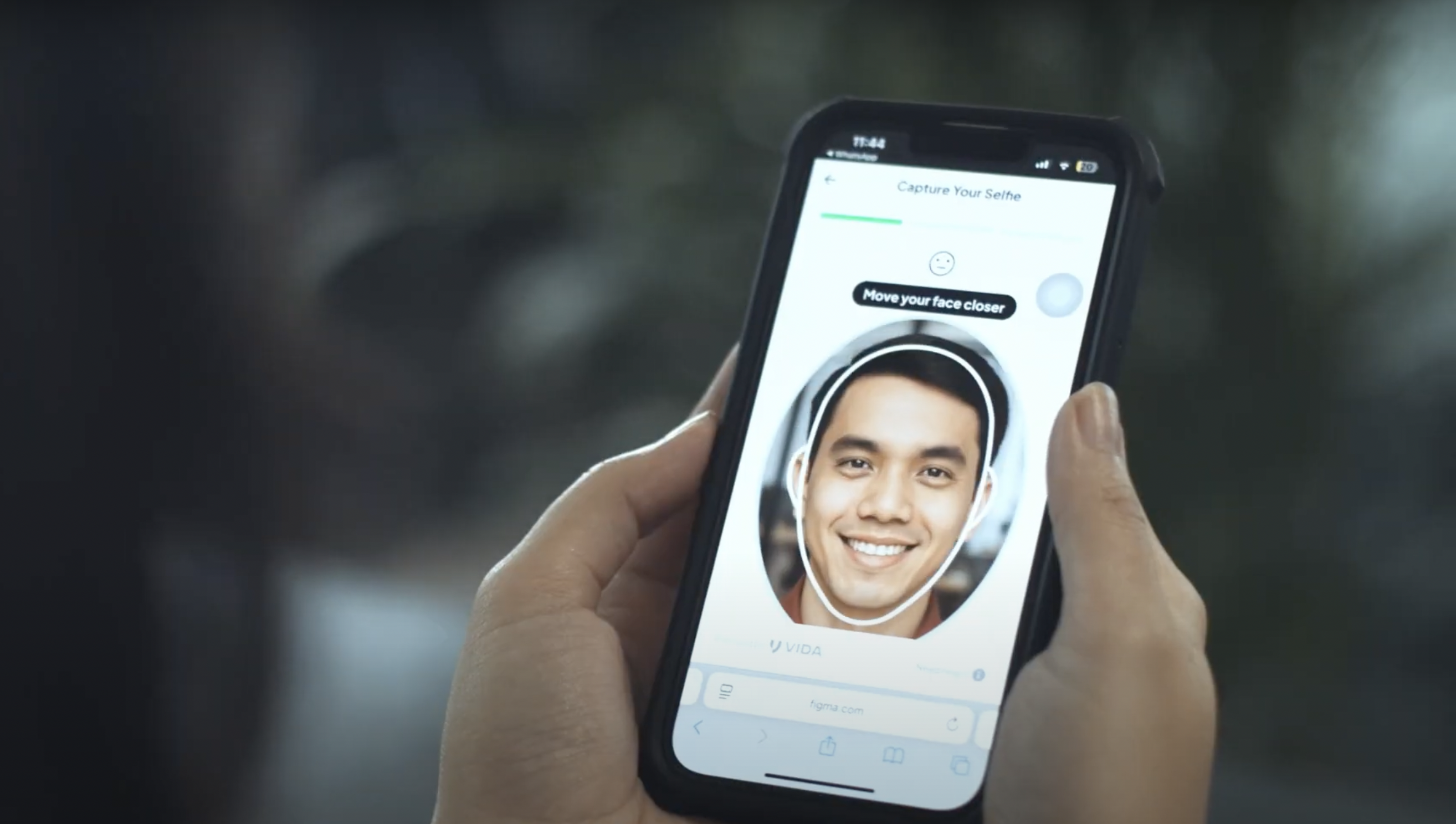
Learn the importance of face verification platforms, how they differ...
May 02, 2025

Although OTP is designed for security, it can still be exploited for...
April 29, 2025

What is a digital identity? Learn more about its types, benefits, and...
April 26, 2025

Discover the different types of secure authentication for digital...
April 05, 2025

2FA might seem inconvenient because it requires two steps to access...
April 03, 2025

Authentication security is essential. Here are authentication apps...
April 02, 2025