How to Calculate THR: Complete Guide with Formulas and Examples
Want to know how much THR (Holiday Allowance) you’ll receive? Here’s...
Employee onboarding helps new hires adapt faster and improve productivity. Learn why onboarding matters and how to create an effective proc...
May 29, 2026
Behind every digital fraud statistic are victims who lose their savings, identities, and sense of security. Through “Faces of Fraud,” VIDA ...
May 20, 2026

Want to know how much THR (Holiday Allowance) you’ll receive? Here’s...
February 23, 2026

Learn about the different types of taxes in Indonesia, their...
February 11, 2026

Unpredictable medical costs make it essential to consider health...
February 05, 2026

Choosing the best car insurance usually comes down to your needs and...
February 05, 2026

Learn about the different types of digital documents you'll...
February 04, 2026

Confused about how to file a car insurance claim? Check out this...
February 04, 2026
.jpeg)
AI-powered attacks—such as large-scale deepfake attacks, synthetic...
February 03, 2026
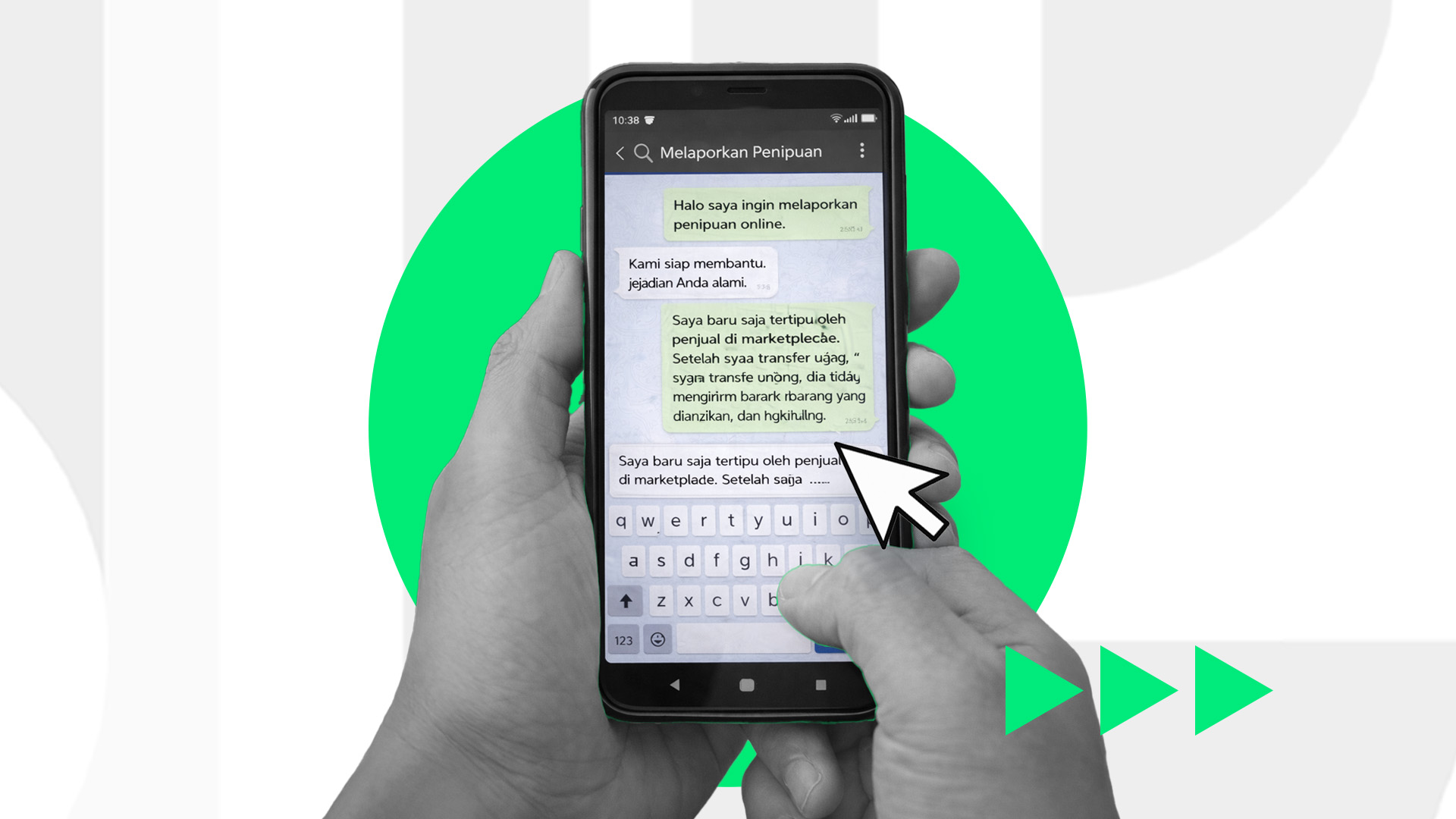
Been scammed online? Learn the important steps to take, what evidence...
February 02, 2026

A complete guide to accessing the Coretax DJP system for taxpayers,...
February 02, 2026

A complete guide to checking your NPWP in Coretax for taxpayers in...
February 01, 2026

Digital scams are becoming increasingly sophisticated and harder to...
February 01, 2026

The Coretax simulation feature can help you understand tax...
January 31, 2026